The physical architecture of the internet, once celebrated as the ultimate borderless commons, is being carved into a patchwork of digital fiefdoms, much like how sovereign wealth funds are quietly buying up global water rights to assert control over essential physical resources. As of mid-2026, the rhetoric of "global connectivity" has been quietly replaced by the tactical realities of "data residency," "sovereign clouds," and "interconnection silos." What we are witnessing is not a temporary policy adjustment but a fundamental rewiring of how packets travel across the globe.
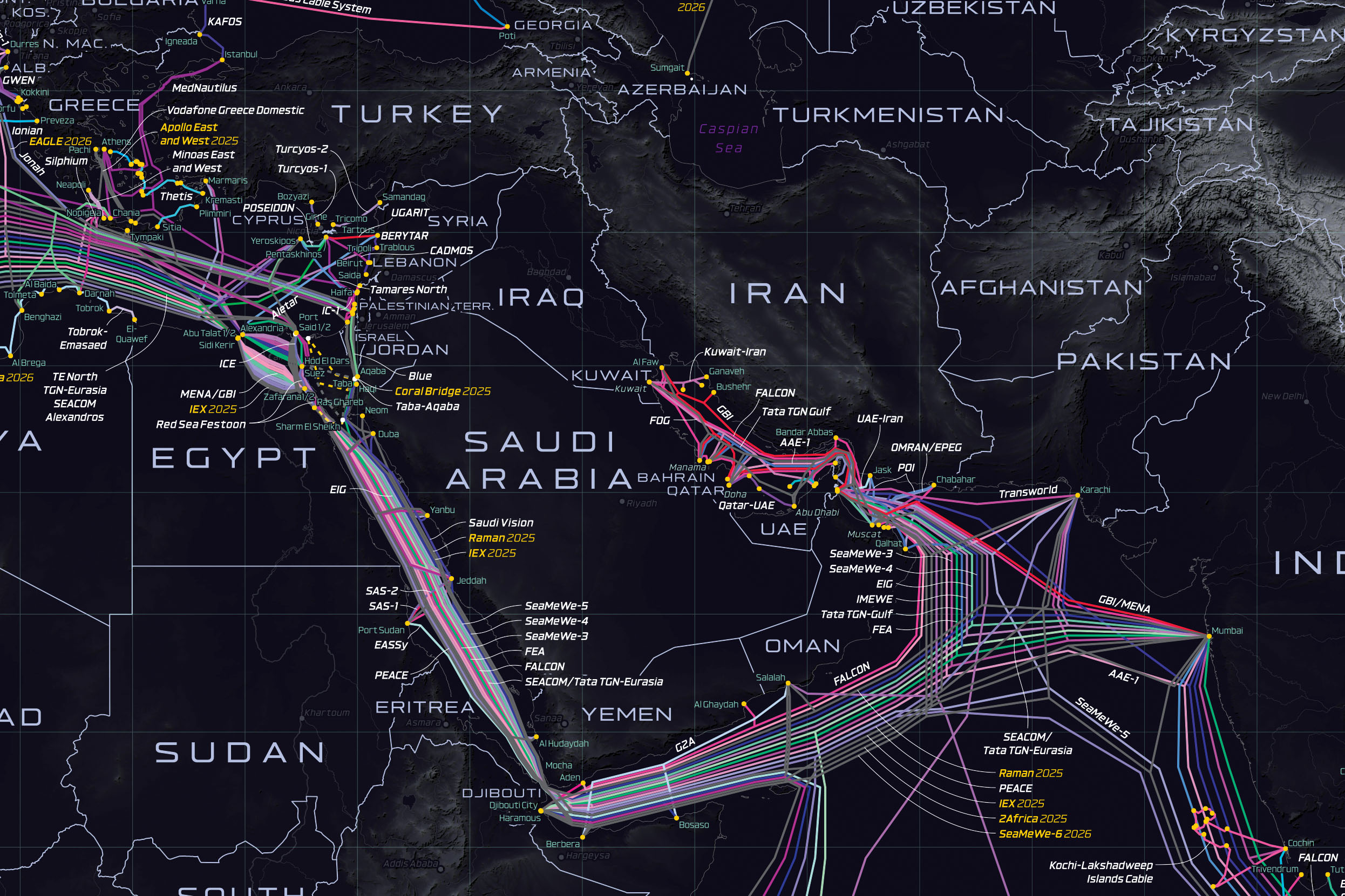
It is no longer just about content moderation or GDPR-style privacy regulations; in the world of high-stakes digital assets, this mirrors institutional liquid staking as a 2026 strategy for yield maximization. It is about the copper, the fiber-optic strands, the subsea cables, and the strategic positioning of localized data centers that essentially act as jurisdictional checkpoints. The internet has hit the wall of the nation-state, creating a complex regulatory environment that mirrors why the deep-sea mining boom is hitting a major regulatory wall.

The Infrastructure of Exclusion
For decades, the internet’s efficiency relied on a "least-cost routing" model. Traffic took the shortest path, indifferent to political boundaries. Today, that model is effectively dead in several key markets. We are seeing a shift toward "geopolitical routing," where national governments mandate that domestic traffic must remain within physical, state-controlled infrastructure.
This has created a massive engineering headache for global CDNs and backbone providers, forcing them to adopt strategies similar to why consumer Wi-Fi fails remote professionals and the shift toward managed networks. In regions like Southeast Asia and parts of the EU, we see "chokepoint compliance." Companies like Cloudflare or Akamai are increasingly forced to maintain "sovereign instances"—separate, localized software stacks that are physically air-gapped from their global management consoles to satisfy local security laws.
The maintenance cost of this fragmentation is staggering, forcing businesses to rethink their operational strategies, much like why dividend investors are shifting to tokenized PropTech REITs to optimize returns. A senior infrastructure engineer at a Tier-1 provider recently posted on a private Slack channel—the logs of which were discussed in a recent NANOG (North American Network Operators Group) forum—noted: "We aren't maintaining one internet anymore. We are maintaining thirty different, incompatible versions of the same service, all fighting for the same latency targets. It’s like trying to keep a dozen different flavors of the same car running with zero shared parts."
The "Sovereign Cloud" Mirage
Governments are pushing for "sovereign clouds"—infrastructure owned or heavily controlled by local entities, ostensibly to protect against foreign espionage. But the operational reality is often far bleaker. When a government mandates that data must be stored locally, they aren't just protecting data; they are creating a honeypot for domestic intelligence agencies.
Take the case of the recent rollout of the "National Data Shield" in a major emerging market in 2026. The intent was data localization. The result, according to various GitHub issues and post-mortem reports filed by foreign SaaS providers, was a complete breakdown in synchronization. Because the local government insisted on owning the root certificates for all traffic within the sovereign cloud, it rendered TLS encryption essentially toothless. Any enterprise trying to use standard, off-the-shelf security tools suddenly found itself "insecure" because it couldn't talk to the global PKI (Public Key Infrastructure).

The Workaround Culture
In the face of these mandates, a "workaround culture" has emerged among developers and sysadmins. In regions where the government has effectively firewalled the local internet, the use of custom, decentralized overlay networks is exploding.
On forums like Hacker News, threads detailing "How to tunnel traffic through non-monitored gateways" are becoming the new standard for DevOps workflows. It’s a cat-and-mouse game. Regulators are now deploying AI-driven traffic analysis to detect these patterns, raising questions about if AI is managing your money and the risks of autonomous investing in 2026. When you try to "fingerprint" every packet to ensure it’s not bypassing a sovereign gateway, latency spikes are inevitable.
The irony is palpable: in the name of "security" and "sovereignty," nations are actively degrading the performance of the very systems they depend on for their digital economies. We are seeing a return to 1990s-era latency figures in regions that were supposed to be "digitally transformed."
Case Study: The Balkanization of the Stack
Consider the "API Diplomacy" crisis of Q1 2026. A major US-based social platform attempted to sync its global user base with a newly opened regional data center to comply with a local sovereignty law. The government demanded that the data center run a localized version of the platform’s authentication API.
The company’s engineers refused, citing security concerns about running proprietary code on government-monitored servers. The government responded by throttling the platform’s traffic to 2G speeds. The platform eventually complied, but only by stripping the regional version of the app of its core features—effectively creating a "lite" version of the platform that was safe for the government but useless for the user.
This resulted in a massive migration of users to local alternatives, which were, in turn, heavily funded by the state. This is the new economic model of 2026: The State as the primary VC and the primary regulator. It’s not a free market; it’s a controlled digital ecosystem.

The Human Cost: Trust Erosion
The most significant victim of the Data Sovereignty Wars is user trust. As the internet fragments, users are becoming increasingly aware that their data is no longer traversing a global, neutral medium. They know that when they post, upload, or browse, they are doing so within the jurisdiction of a local actor.