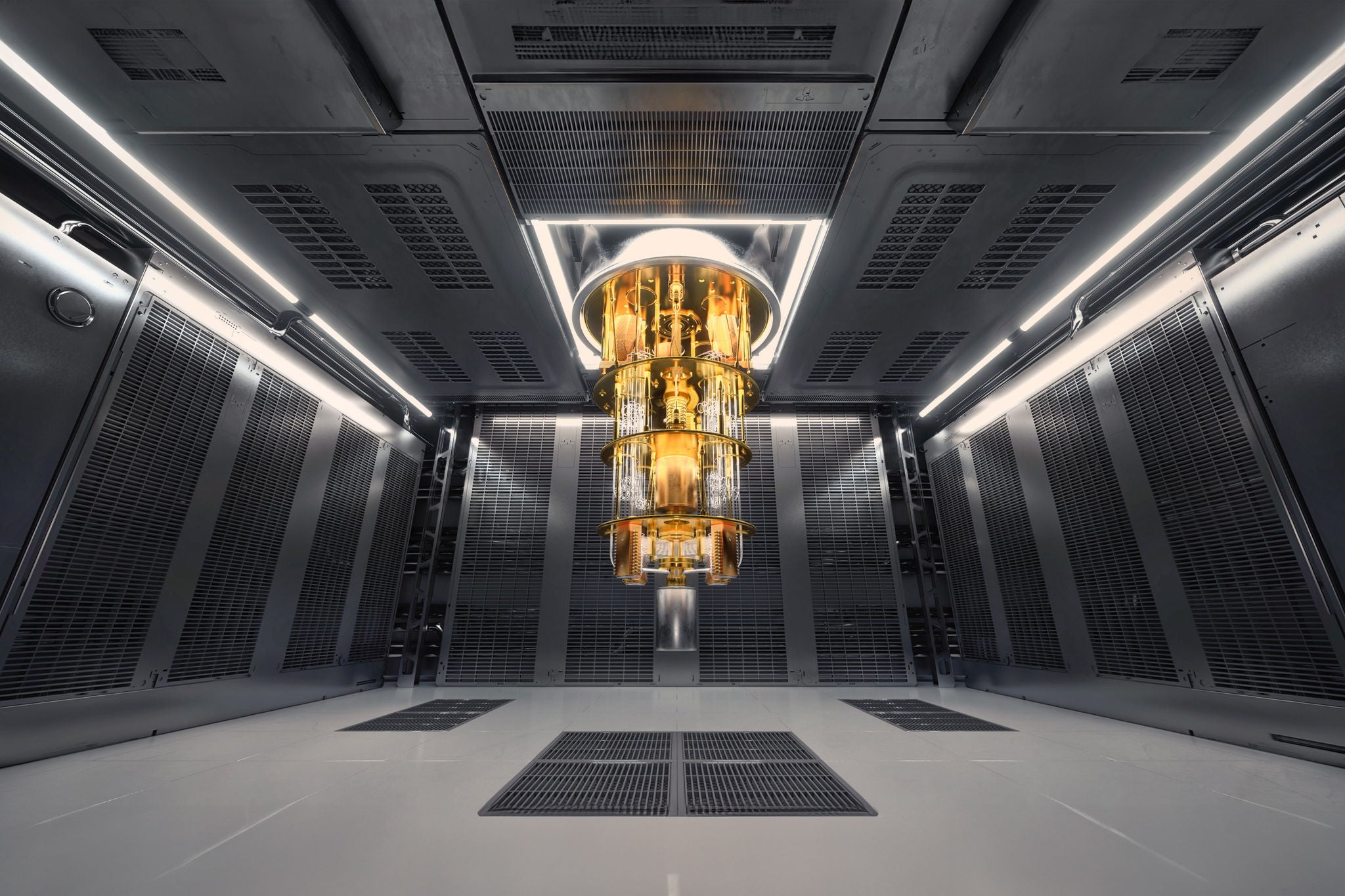
The clock is ticking. Somewhere inside a nondescript data center in Frankfurt, a team of cryptographers and core-banking engineers are stress-testing a lattice-based encryption module against a simulated quantum attack. They are not doing this because quantum computers capable of breaking today's encryption exist yet — they are doing it because, by most credible estimates, they will exist by 2030. And the financial system is not ready.
This is no longer a theoretical exercise confined to academic white papers. In 2026, the race to quantum-proof the global financial infrastructure has moved from boardroom curiosity to boardroom emergency.
The Threat Is Concrete — and the Timeline Is Closing
The concern centers on a specific class of quantum algorithms. Shor's algorithm, developed by mathematician Peter Shor in 1994, can theoretically factor large integers exponentially faster than classical computers — effectively rendering RSA-2048 and elliptic-curve cryptography (ECC), the twin pillars of modern banking security, obsolete.
According to the U.S. National Institute of Standards and Technology (NIST), which finalized its first set of post-quantum cryptographic standards in August 2024, the transition window for critical infrastructure is estimated at five to ten years. That puts the outer boundary firmly at 2034 — but financial regulators are not waiting that long.
The Bank for International Settlements (BIS) published a working paper in early 2025 estimating that approximately $22 trillion in daily global payment flows are currently protected by encryption schemes vulnerable to quantum decryption. The European Central Bank has flagged quantum risk as a Tier-1 systemic concern in its 2025–2030 Digital Finance Strategy.
"Harvest Now, Decrypt Later" — The Hidden Urgency
Here is the part that most people miss: you don't need a quantum computer today to create a quantum-era problem today.
State-level threat actors are already engaged in what security professionals call "harvest now, decrypt later" (HNDL) attacks — intercepting and archiving encrypted financial communications now, with the intention of decrypting them once sufficiently powerful quantum hardware becomes available. Sensitive interbank correspondence, sovereign debt transaction records, and cross-border SWIFT messages encrypted today could be exposed within a decade.
"The misconception is that this is a future problem," said Dr. Lena Fischer, a quantum cryptography advisor at Deutsche Bundesbank, in a February 2026 symposium. "If your data has a confidentiality horizon of more than seven years — and a great deal of financial data does — you are already operating inside the threat window."
What "Overhauling Core Systems" Actually Means
Replacing encryption in a bank is not like updating a software patch. Core banking systems at major institutions are layered, deeply integrated, and often decades old. The average G-SIB (Globally Systemically Important Bank) runs between 15 and 40 distinct legacy systems, many built on COBOL codebases from the 1980s.
Migrating these systems to post-quantum cryptography (PQC) standards — specifically, NIST-approved algorithms like CRYSTALS-Kyber (for key encapsulation) and CRYSTALS-Dilithium (for digital signatures) — requires:
- Full cryptographic inventory audits: identifying every point in the system where encryption is applied, often numbering in the thousands
- Hybrid cryptographic frameworks: running classical and PQC algorithms simultaneously during transition to avoid compatibility failures
- Hardware Security Module (HSM) replacements: many existing HSMs cannot support lattice-based algorithms without firmware or physical upgrades
- Third-party vendor compliance: payment processors, cloud providers, and SaaS vendors must also be PQC-compliant, creating a cascading dependency chain
JPMorgan Chase disclosed in its 2025 Annual Report that it had completed a cryptographic bill of materials (CBOM) across its entire infrastructure — a process that took 18 months and involved over 1,200 engineers. The bank has allocated $400 million toward its quantum-readiness program through 2028.
HSBC, meanwhile, has been piloting a quantum key distribution (QKD) network across its London-Hong Kong corridor since Q3 2025, using fiber-optic photon transmission to create theoretically unbreakable key exchanges. QKD, while promising, remains expensive and geographically constrained — it cannot be scaled globally through the internet alone.
The Regulatory Pressure Layer
Financial regulators are no longer offering guidance — they are issuing mandates.