The email landed in Marcus Trevino's inbox on a Tuesday afternoon last spring, and it wasn't from a regulator or a federal agency. It was from his commercial insurance carrier — a boutique firm out of Denver that had been covering his 40-person logistics company for six years. The message was polite but unambiguous: before policy renewal in ninety days, Trevino's company would need to undergo a third-party zero-trust security audit, or coverage for AI-related cyber incidents would be quietly dropped from the policy.
"I thought it was a mistake," Trevino said. "We're not a tech company. We move freight."
He's not alone in his confusion — or in being caught off-guard by how quickly a niche insurance underwriting conversation has become an operational mandate for thousands of small and mid-sized businesses across North America and Western Europe.
The Quiet Shift Nobody Warned SMEs About
Over the past eighteen months, a cluster of boutique and regional insurance carriers — not the massive generalist players like Zurich or AXA, but the smaller, specialized firms that underwrite heavily in professional liability, commercial cyber, and technology errors-and-omissions — have begun embedding what amounts to security architecture reviews directly into their renewal processes.
The trigger isn't arbitrary. Since late 2024, AI-assisted cyberattacks have structurally changed the threat landscape in ways that older underwriting models were never designed to price. Phishing kits that previously required human social engineering now run autonomously. Business email compromise schemes now operate at machine speed. Ransomware operators use AI-powered reconnaissance to identify vulnerable SME networks faster than most small firms can even detect the intrusion.
Insurance actuaries who spent 2023 and early 2024 modeling AI risk in theoretical terms are now staring at actual claims data — and the loss ratios are moving in uncomfortable directions.
"The carriers doing this aren't being punitive. They're responding to claims they've already paid out. When your book of SME cyber policies starts bleeding, you either reprice the risk or you start demanding the policyholder manages it differently." — A commercial insurance broker who has worked with mid-market carriers for over a decade
What Zero-Trust Actually Means in This Context (And Why the Label Is Doing a Lot of Work)
Here's where the operational reality gets complicated — and where some legitimate frustration inside the SME community is well-founded.
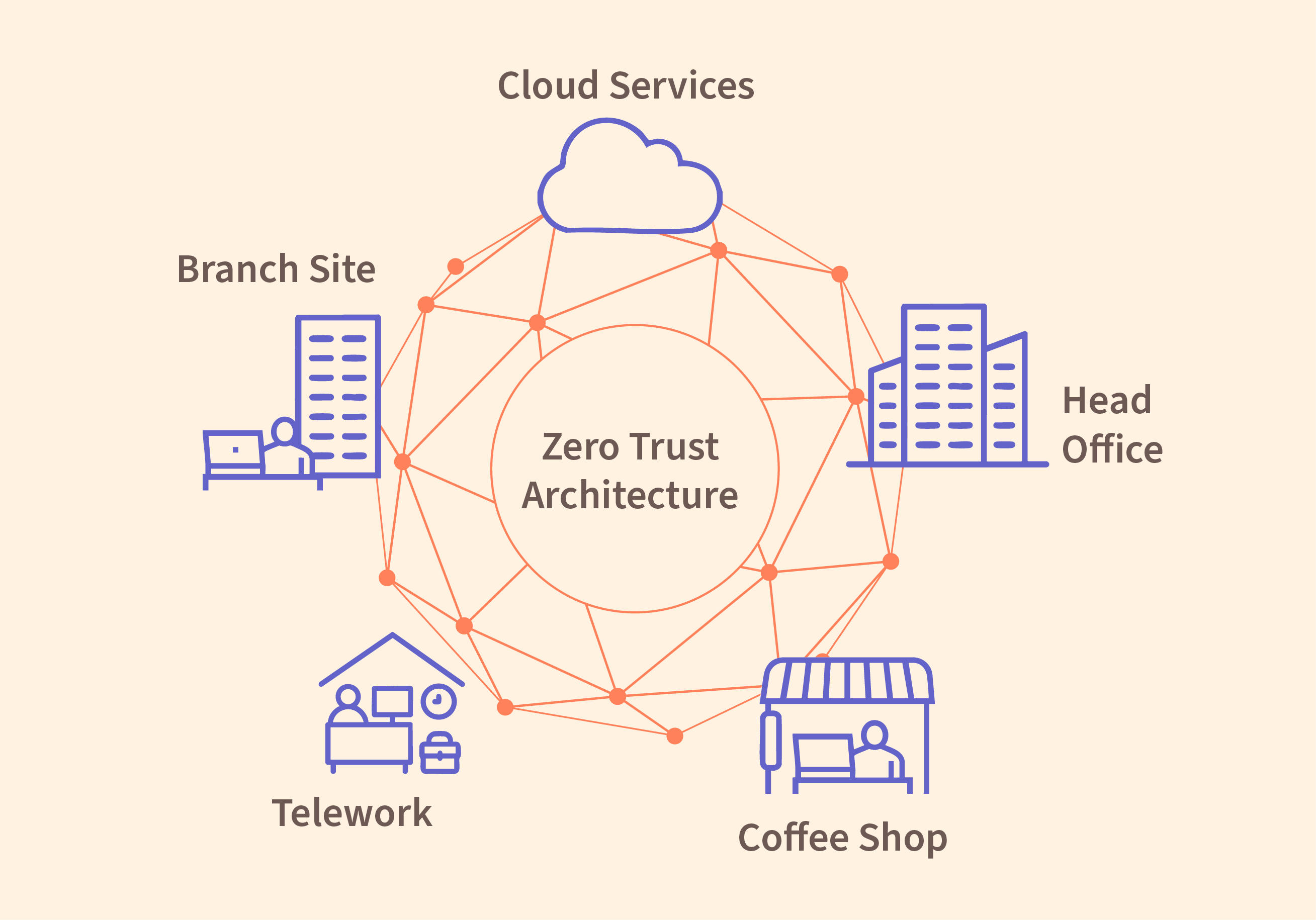
"Zero-trust" as a security framework is, depending on who you ask, either a rigorous architectural philosophy involving microsegmentation, continuous identity verification, and least-privilege access enforcement, or a marketing term that vendors have stretched to cover nearly anything involving multi-factor authentication and a network diagram. The insurance industry's adoption of the term hasn't exactly clarified things.
A GitHub thread on a popular DevOps community forum from earlier this year captured the confusion well. One commenter: "My insurer sent over a 'zero-trust compliance checklist' that basically asked whether we had MFA turned on and if we reviewed access logs quarterly. That's not zero-trust. That's just not being completely reckless."
The audits being mandated by boutique carriers vary wildly in scope and rigor. Some require a formal third-party penetration test with a written remediation report. Others involve a forty-five-minute video call with a "security advisor" who is, in some cases, a subcontractor hired by the insurance firm itself — a structural arrangement that creates obvious questions about independence and incentive alignment.
The SME experience on the ground is fragmented. Some businesses report that the audit process was genuinely useful, surfacing misconfigured cloud environments and forgotten admin accounts with broad permissions. Others describe an exercise that felt largely performative — a compliance checkbox that costs between $3,000 and $12,000 in consultant fees, produces a report that mostly gets filed away, and changes very little about how the company actually operates.
The Boutique Carrier Calculus
Why are smaller, specialist carriers leading this shift rather than the large generalist insurers? Part of it is concentration risk. A boutique firm writing heavily in, say, professional services or healthcare-adjacent SMEs has a narrower, more correlated book of business. One bad wave of AI-assisted attacks hitting its specific sector can create outsized claims exposure. The large carriers are diversified enough to absorb more shock before they feel compelled to act.
There's also a competitive dynamic at work. Boutique carriers positioning themselves as sophisticated underwriters of "managed risk" — rather than just price-competitive commodity coverage — have an interest in being seen as ahead of the curve on AI threat modeling. Mandating zero-trust audits is partly genuine risk management and partly a market positioning statement: we take this seriously, and we expect you to as well.